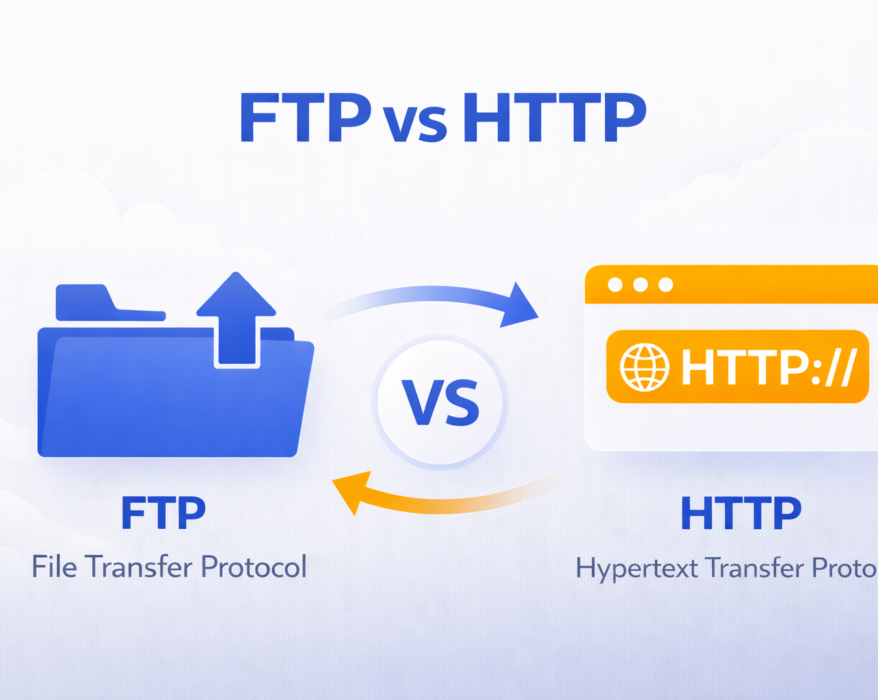
FTP vs HTTP: Understanding the Key Differences
Today we will see what exactly is FTP (File Transfer Protocol) and how does it compare to the newer...
New SSL Certificate Renewal Rules
For years, SSL certificates have been essential for securing websites, protecting user data, and building trust online. But the way these...
How does OSI Application layer 7 DDoS attack work?
As cyber threats evolve, Distributed Denial of Service (DDoS) attacks have become more sophisticated and stealthy. Among the most complex...
HTTP vs HTTPS: Why every website needs HTTPS today
In today’s digital age, securing information online has become more important than ever. One...
Top 10 cURL Commands for Web Developers
As a web developer, one tool you’ll frequently turn to for interacting with servers, testing APIs, and debugging is cURL. Whether...
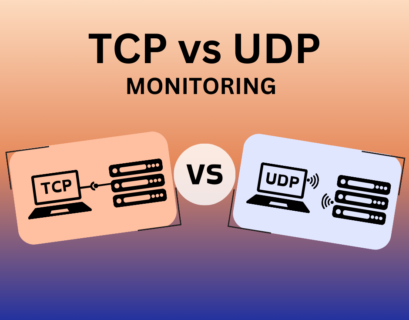
Comprehensive Guide on TCP Monitoring vs. UDP Monitoring
Why does the battle between TCP monitoring vs UDP monitoring matter in the world of network management? In this guide, we’ll delve...
What is a Certificate Signing Request (CSR) and How to Generate It?
Securing your website with SSL/TLS certificates is crucial for protecting sensitive data and...
HTTP flood attack – What is it and How to prevent it?
In a world where an online presence is crucial, an HTTP flood attack poses a significant threat, overwhelming websites with an onslaught of...
SFTP Fundamentals: A Deep Dive into Secure File Transfer Protocol
In a world where data is constantly in motion – whether you’re sending files to cloud servers, collaborating with remote teams, or...
What is an SSL certificate and do we need it?
An SSL certificate is essential for securing websites, encrypting sensitive data, and building...