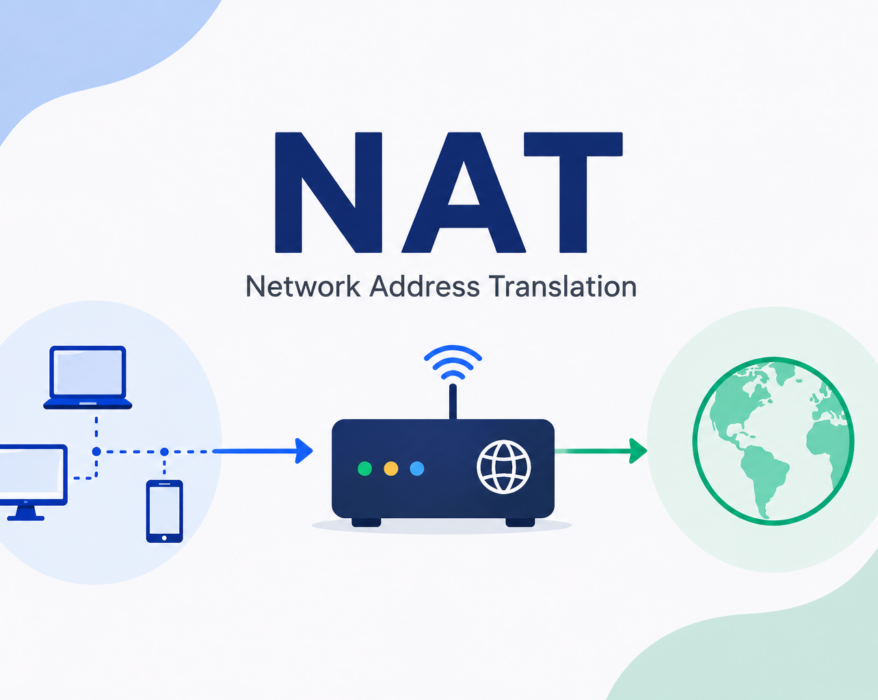
NAT (Network Address Translation): How It Works and Why It Matters
NAT (Network Address Translation) plays a major role in how devices connect to the Internet today....
What is ICMP (Internet Control Message Protocol)?
The ICMP (Internet Control Message Protocol) is a network layer protocol and also a supporting protocol in the Internet protocol suite. It...
Understanding Phishing Attack and How to Stay Protected
In today’s digital age, the internet has become an integral part of our daily lives, enabling us to connect, shop, and conduct...
Understanding the HTTP status codes
Any now and then, when we are browsing the internet, we get one of those – error 500 or error...
Single Point of Failure (SPOF): How to Identify and Eliminate It?
The risk of a Single Point of Failure (SPOF) has become a critical concern in interconnected modern businesses and technologies. The...
R.U.D.Y. (R U Dead Yet) Attack Explained
In the ever-evolving landscape of cybersecurity, new threats constantly emerge, challenging the robustness of online systems. One such...
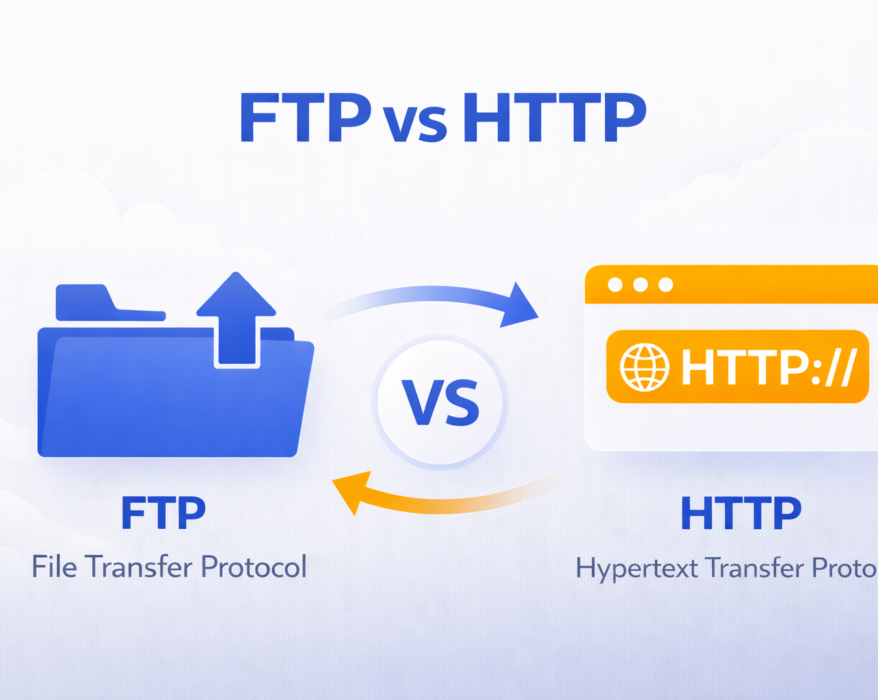
FTP vs HTTP: Understanding the Key Differences
Today we will see what exactly is FTP (File Transfer Protocol) and how does it compare to the newer...
Telnet Explained: What Is It and How It Works?
In the world of computing and networking, Telnet has been an essential tool for connecting computers and devices remotely. Despite being an...
Decoding Error 500: Understanding, Preventing, and Resolving the Internal Server Error
Error 500, the “500 Internal Server Error,” casts a shadow in the digital landscape, marking moments of unexpected turbulence...
Top 10 cURL Commands for Web Developers
As a web developer, one tool you’ll frequently turn to for interacting with servers, testing...