What is a DNS outage (DNS downtime), and how to avoid it?
Knowing what DNS is can already show you the answer to what DNS outage is. The clients won’t resolve your domain name, so they will get...
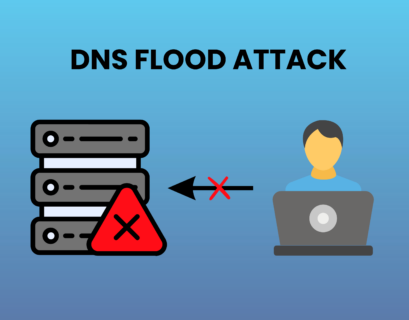
DNS flood attack explained in details
In the ever-evolving landscape of cyber threats, a DNS flood attack stands out as a formidable challenge for businesses and individuals...
What is Enterprise DNS?
The Enterprise DNS is a high-level class of DNS service. Its purpose is to serve large companies....
Botnet – what is it, and how does a Botnet attack work?
Cybercriminals often use Botnet for their malicious purposes. That way, they build their army of devices and execute massive attacks. So...
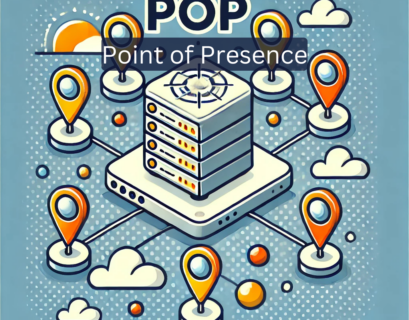
What is a Point of Presence (PoP) and Why Does It Matter?
Every time you visit a website, stream a video, or access an online service, your request travels through multiple network points before...