What is SNMP Vulnerability? How to stay protected?
SNMP Vulnerability is a hidden risk lurking in many network infrastructures. The Simple Network...
10 Steps to Prevent Ransomware attack
The Ransomware attack is one of the most destructive types of cyberthreats today. It targets individuals, businesses, and even governments...
Cron Job Monitoring: A Basic Overview
In the world of server management and automation, cron jobs play a pivotal role. These time-based job schedulers in Unix-like operating...
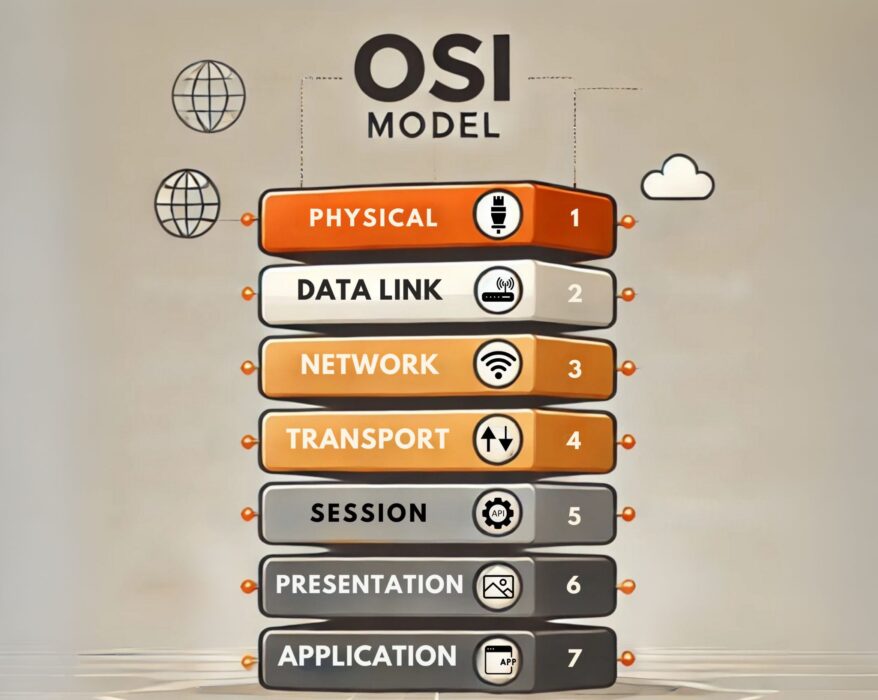
How do OSI Model layers work in computer networking?
In the vast realm of networking, the Open Systems Interconnection (OSI) Model stands as one of the...
The Ultimate Guide to Web Performance Monitoring
In the digital age, a website’s performance is crucial for business success. Slow-loading pages, downtime, or security breaches can...
What is DNS filtering? Do you need it?
DNS filtering helps organizations keep networks and users safe by blocking access to malicious and harmful websites. It also allows...
What is a Certificate Signing Request (CSR) and How to Generate It?
Securing your website with SSL/TLS certificates is crucial for protecting sensitive data and...
DNS flood attack explained in details
In the ever-evolving landscape of cyber threats, a DNS flood attack stands out as a formidable challenge for businesses and individuals...
HTTP flood attack – What is it and How to prevent it?
In a world where an online presence is crucial, an HTTP flood attack poses a significant threat, overwhelming websites with an onslaught of...
SFTP Fundamentals: A Deep Dive into Secure File Transfer Protocol
In a world where data is constantly in motion – whether you’re sending files to cloud...